Utilizing Self-Organizing Heterogeneous Networks
| ✅ Paper Type: Free Essay | ✅ Subject: Engineering |
| ✅ Wordcount: 3831 words | ✅ Published: 31 Aug 2017 |
A Disaster-Resilient Modern Cellular Network: Utilizing Self-Organizing Heterogeneous Networks, Device-to-Device Communication enabled LTE-Advanced
Abstract
The goal of modern communication networks is to keep every corner of the world connected at all times. This goal is of utmost importance especially during a disaster. Today’s mobile communication networks fail to showcase fast disaster resilience due to the lack of a distributed communication architecture that would work even if a part of the network fails. With current technological advancements, this resilience can be achieved by creating an overlay of various techniques. Heterogeneous Networks (HetNet) and Internet of Things (IoT) play significant roles in the next generation 5G networks. Having this in mind, this paper discusses how Self Organizing Networks (SON) when applied to HetNet, and a distributed Device-to-Device (D2D) communication enabled architecture when applied to Long Term Evolution – Advanced (LTE-A), can strengthen the disaster resilience of a modern cellular network. Self-configuring, self-optimizing and self-healing heterogeneous small cell networks reduce the need for human intervention and ensure reliable communication during calamities. A D2D type communication is important because in most cases, physical damage to operators’ network elements is the cause for network failure. Hence there is a need to be able to communicate emergency messages without total dependency on a carrier’s network. The means of achieving these two goals will be addressed in this paper.
I. Introduction
The earliest forms of communications were intended to send emergency messages during wars. While communication technology has evolved from sending pigeons to next generation 5G, the industry has not been able to ensure perfectly reliable communication for disaster-struck regions with the unaffected areas during times of emergency. The existing methods for emergencies such as the earthquake and tsunami warning system (ETWS), Public Safety Networks, only serve the purpose of communicating broadcast messages to public and information sharing among officials. However it is important to also have a reliable communication means between victims in affected areas and the outside world. In 2011, around 29,000 eNBs were damaged during the Great East Japan Earthquake and Tsunami, which caused network outage and affected communication of safety messages and emergency requests [12].
Problems in wireless networks during disaster scenarios include increase in traffic beyond the network’s capacity, physical damage of network components including backhaul, unnecessary handovers due to improper neighbor list and limited availability of human resources [1]. The methods discussed in the paper will address these problems.
A Heterogeneous Small Cell Network (HSCN) is one in which there is an umbrella created by the macro cell and small cells are deployed within the region to help fix coverage gaps and capacity needs [14]. The co-ordination of different cells within the same region without interfering is the challenging part of an HSCN. D2D communication is one in which the User Equipment (UEs) can exchange information directly.
This paper will start by discussing the architecture of a SON-enabled Disaster – Resilient HSCN (DRHSCN). We will discuss how self-configuration of power, automatic neighbor relation (ANR), Physical Cell Identity (PCI), self-optimization of coverage, capacity, mobility robustness and self-healing capabilities help in achieving minimal human intervention during disasters [1]. The next section of the paper will discuss how a multihop D2D communication system realized through smartphones relay can help in disaster resilience [3]. We will then discuss how the current LTE architecture can be made distributed in order to minimize the dependency between User Equipment (UE) and the core network [2]. We will discuss how D2D communication can help in this regard and increase the disaster resilience of an LTE-A network [2].
II. Utilizing SON in DRHSCN
The primary purpose for using SON in Disaster Resilient Heterogeneous Small Cell Networks (DRHSCN) is to reduce the operational expenditure (OPEX) and human intervention. The DRHSCN architecture as shown in Figure 1 [1] consists of a macro cell and several small cells (femto cells) within the macro cell. Satellite link provides the backhaul. The SON entity of the network is present on the base station side. The Heterogeneous evolved Node B (HeNB) serves the femto user equipment (FUE) while the macro base station serves the macro user equipment (MUE).
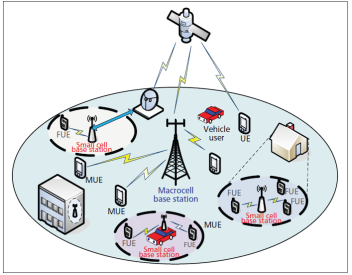
Figure 1. Architecture of DRHSCN [1]
During disasters, there will need for deployment of new nodes such as cellular on wheels (CoW), adaptation of the existing nodes to the changes, and healing of the nodes that were damaged physically. Self-configuration means a newly added node during a disaster scenario automatically selects the network parameters and schemes such as physical cell ID (PCI), power configurations, neighbor lists and other basic settings needed for proper operation [4]. The newly added nodes are configured into the network and then the existing nodes involve in self-optimizing as a reaction to the environmental changes caused by the disaster. Self-optimization means automatically changing the radio resource management parameters such as power parameters (pilot, control and data), tilt, azimuths, handover management parameters, and others needed to optimize the performance of the network [4].
- Self-Configuring new nodes
We will discuss the methods for self-configuring the transmit power, physical cell ID and Automatic Neighbor Relation (ANR) in DRHSCN.
Let us assume a new HeNB is entering the network and its boundary ends where the path loss is 2 dB from the HeNB. When it powers on, the HeNB will receive Reference Signal Received Power (RSRP) measurements of the macro eNB as well as other HeNBs in the vicinity. Based on this self-discovery, the HeNB will configure a suitable transmit power to mitigate the co-channel interference with the macro or other small cells [1]. A FUE will be covered by the HeNB if Signal to Interference and Noise Ratio (SINR) from the HeNB is above 3dB. An MUE will be served by the macro eNB if SINR from macro eNB is above 1dB. Based on these assumptions, the self-configuration will make sure that for FUE outside the 2dB boundary, SINR is below 3dB. For MUE outside the 2dB boundary, SINR is above 1dB. This way the HeNB cannot affect the MUE outside its boundary [1].
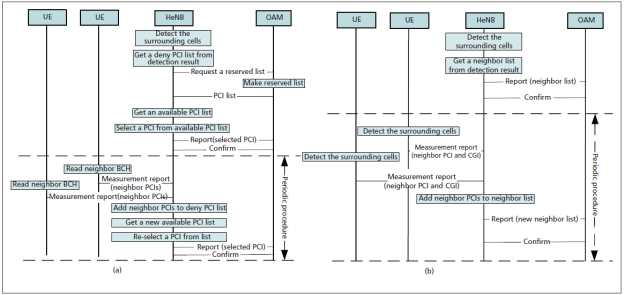
Figure 2. (a) Self-configuration of PCI [1] (b) Self-configuration of ANR [1]
A physical cell ID needs to be unique for each cell in its operating area in order to avoid collision and confusion. Since the primary and secondary synchronization signals (PSS, SSS) are based on the PCI, any collision would result in synchronization problems. There are only 504 possible PCIs [4]. Hence in a dense deployment of heterogeneous networks, it is difficult to guarantee uniqueness. Instead of manually configuring PCI during network planning or randomly selecting a PCI, an automatic PCI selection algorithm [1] as shown in Figure 2a [1] would result in lesser collisions and confusions in a disaster scenario. The HeNB first detects neighbors in its vicinity and composes a deny list. It then requests a reserved list from the SON-enabled OAM (Operations, Administration, and Maintenance) system. Based on these, an available PCI is selected and confirmed with the OAM. It is a periodic procedure and the HeNB reselects its PCI based on the neighbor PCIs seen in UE measurement reports.
In order to ensure handovers are managed properly in the absence of human resource during disasters, an Automatic Neighbor Relation (ANR) feature should be added. This enables the self-configuration of the Neighbor Relation Table (NRT) and deletion of unnecessary neighbor relations (NR). The algorithm is shown in Figure 2b [1] and is very similar to the PCI selection algorithm. Instead of a PCI list, a neighbor list is composed. The neighbor PCI and Cell Global Identity (CGI) are obtained from the UE measurement reports. ANR reduces the need for handover selection from a long neighbor list by removing unnecessary NR periodically. [1]
- Self-Optimizing existing nodes
Self-optimization in the existing HeNB in DRHSCN is achieved in two ways – Mobility Robustness Optimization (MRO) and Coverage Optimization.
In a heterogeneous network, the occurrence of unnecessary handovers due to complex mobility patterns and cell boundaries, results in large consumption of resources which cannot be afforded especially in a disaster scenario. The purpose of self-optimizing handover (HO) parameters is to detect such unnecessary handovers and to avoid them while not compromising on handover failure rate. A Mobility Robustness Optimization algorithm is proposed for a DRHSCN [1]. A cost function is first calculated as a weighted sum of five types of handovers [5]. These include ping-pong handover which return the HO back to the serving cell, early handover when Radio Link Failure (RLF) occurs since the HO was executed earlier than required, late handover when the HO is processed too late which results in RLF, continuing handover when the HO after execution is immediately is handed over to another cell which is not the serving cell, wrong handover when the HO was made to the wrong cell resulting in RLF [6].
In order to optimize the handover process, each HeNB has a timer which starts when handover complete message is received from UE. This timer stops as soon as an RLF occurs or is reported by other eNBs/HeNBs. From the UE status after RLF the HeNB will be able to recognize if it was a late, early or wrong handover, or call drop. Based on the performance metrics collected by a single eNB/HeNB, the parameters are optimized [1]. As shown in Figure 3 [1], the optimized parameters are calculated based on the cost function. This calculation is repeated iteratively after detecting unnecessary, too late, too early and wrong handovers, and fixing the weights of the cost function accordingly. The SON-enabled OAM (Operations, Administration, and Maintenance) system collects the performance reports. The RLF and unnecessary HO are reduced significantly by the optimization algorithm which will help in efficient handovers during disasters when the HeNB are randomly deployed [1].
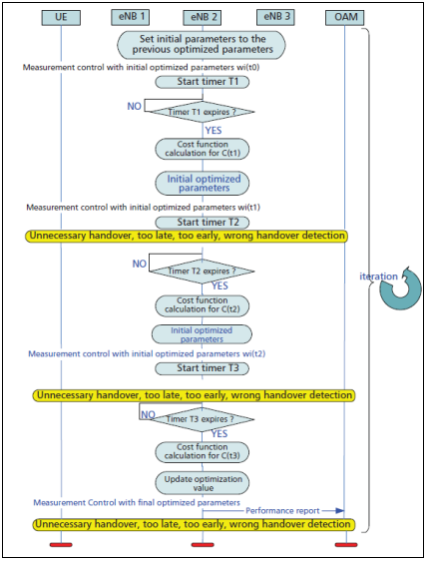
Figure 3. Mobility Robustness Optimization (MRO) [1]
Coverage optimization is done by adaptively choosing the cell boundary. This is important in a disaster scenario because fast random deployments of small cells do not take into account the interference caused by the small cells with macro cells which will reduce the performance of the DRHSCN. In the self-configuration phase, we created fixed boundaries based on RSRP measurements of eNB and other HeNBs. This boundary is not realistic since we will deploy small cells indoor such as in buildings. The RSRP measurements of the FUE during the self-optimization phase will help in determining a realistic coverage radius. Large changes in RSRP is observed when the FUE enters or leaves a building due to penetration loss associated with walls. The algorithm given in Figure 4 [1] shows how after self-configuration, either an adaptive or fixed boundary is chosen based on whether a house boundary was got from the decision module. This process is iteratively applied and an optimal boundary is chosen. The performance analysis of the power self-configuration and coverage self-optimization algorithm together shows better macro and small cell coverage. It helps provide better coverage and manage capacity efficiently [1].
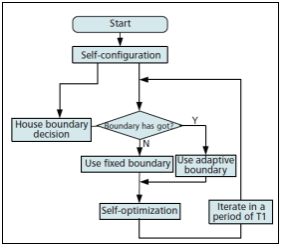
Figure 4. Coverage and Capacity Optimization [1]
- Self-Healing triggered by failed nodes
Self-healing is the process of handling the coverage gaps or capacity overloads resulting from the failure due to physical damage of a base station (either macro or small cell) during disasters [1]. Self-healing consists of automatic fault detection, fault classification and cell compensation schemes [7]. Figure 5 [7] shows the flow chart of a self-healing process. Fault classification into degraded (sub-optimal operation), crippled (major faults causing low SINR) or catatonic cells (complete outage) can be done using Bayesian systems to determine type of fault with certain probability [9]. Learning algorithms are important to make the detection more intelligent by having a log of faulty alarm detections. The Trigger Conditions of Self-Healing (TCoSH) satisfy when anomalies occur for a particular duration and cause sufficient performance degradation. The logical steps for self-healing are provided by Third Generation Partnership Project (3GPP) in [8]. The compensation schemes, depending on type of fault, might involve automatic reconfigurations which would direct the neighbors to up tilt antennae, increase power, or enable relay-assisted handover [10]. It is critical to continue monitoring the faulty base station through X2 interface to check if it has recovered, so that neighbors can return to their optimal configurations. Much research is needed in self-healing in terms of the various learning, classification, and compensation algorithms before it can be deployed practically [7].
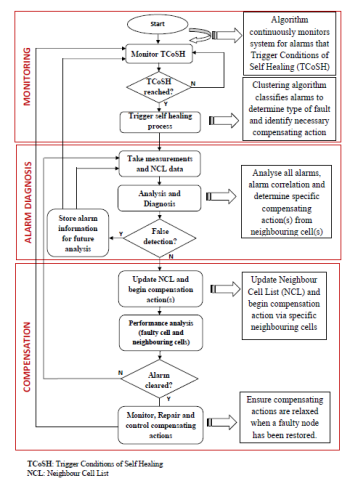
Figure 5. Self-Healing Process [7]
III. D2D communication during disasters
In the previous section, we discussed how a SON-enabled DRHSCN implementation can help operate a 4G network reliably and efficiently during disasters. However, we need to note that the dependence on cellular operators’ networks is high in a DRHSCN. During a disaster, the physical damages caused to the operator network in a significantly large area, are difficult to be handled using self-healing alone. Hence there is a need for a decentralized network architecture as an overlay over DRHSCN that will ensure reliable communication of emergency messages.
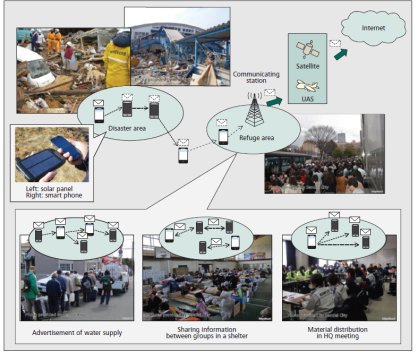
Figure 6. D2D communication during disasters [3]
- Access and Network technologies in D2D communication
In this sub-section we will discuss a multi-hop D2D communication realized using relay by smartphones [3]. As a minimum requirement, unacknowledged, best effort delivery of small packets of messages such as text, voice should be possible. The types of messages may be emergency communication between affected areas and outside world, broadcast messages to the affected areas, local information sharing within refugee areas, etc. as shown in Figure 6 [3]. The interconnection of the D2D network with the outside world can also be achieved through Satellite, unmanned aircraft system (UAS), etc. [3]. The various technologies that can be used in multihop D2D communication as shown in Figure 7 [3] will be discussed next.
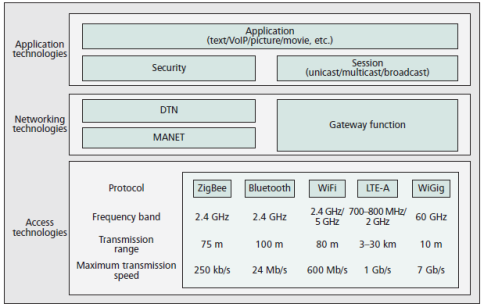
Figure 7. Technologies in D2D communication [3]
The wireless access technologies need not be limited to one. Multiple technologies such as Bluetooth, WiFi, Zigbee, LTE-A, WiGig (Wireless Gigabit) can be used based on the environment, data needs, physical distance, spectrum availability. The developments in mobile equipment technologies such as battery technology, antenna design techniques enable the use of various wireless interfaces on a single mobile terminal [3]. Bluetooth, WiFi and Zigbee are used currently. While WiGig has the advantage of being de-centralized and having high speeds (up to 7 Gbps for 60 GHz bandwidth), it is a short range technology (10m). LTE-A has the advantage of having a good channel quality and lesser interference due to a base station acting as controller. To overcome the disadvantage of dependence on operator network during disasters, we will discuss a decentralized D2D communication architecture for LTE-A in the next sub-section.
The networking (routing) technologies used in smartphone relay cannot be fixed, like in other multihop communications due to the unpredictable mobility of the terminals. Hence each device selects its own routing method based on its situation. Hence integrating various routing technologies is inevitable. For a stable dense mesh network such as WiFi ad hoc, which is are almost immobile, mobile ad hoc networks (MANET) type routing is preferred. MANET sends a message via an established path from source to destination. Delay/disruption-tolerant networks (DTN) is suitable for both single and mutihop communication since it is a network layer technology [3]. For wireless access technologies that work on a single hop such as Bluetooth, Zigbee, DTN-type routing has to perform multihop through various single hops. Since the best type of routing depends on the scenario, implementing a fusion of the two routing types would be the most efficient.
Interconnection of the multihop D2D communication system with external networks such as satellite, movable and deployable resource units (MDRU) [11], unmanned aircraft systems (UAS) is possible. Longer distance communication with areas not affected by the distance is possible through such interconnection. The gateway between the D2D system and outside networks filters out redundant messages received from DTN type routing which tends to send duplicates [3]. The gateway should advertise its presence so that the terminals can direct their messages to it. For certain applications, it is important to ensure confidentiality, integrity, and availability. Hence a security functionalities are added. In order to ensure that all types of smartphones can participate in the D2D communication, all operating systems (Android, iOS, Windows, etc.) should be compatible. In order to ensure independency from cloud services, it is suggested that the terminals have a mutihop D2D mode for emergency purposes. In [3], a prototype based on fusion of MANET and DTN routing technologies was developed and its performance was tested to be good.
- D2D communication enabled decentralized LTE-A architecture
The dependencies between the UE, eNB and Evolved Packet Core (EPC) reduce the resilience and flexibility of a 4G network. We will discuss a D2D enabled LTE-A architecture that will reduce this dependency [2]. The EPC is an all-IP core network that performs the access control, authentication, etc. Failure of any entity within the EPC can cause a cascading effect and might take long time to fix. A novel software architecture, which virtualizes certain fundamental EPC services and resource management functions within the eNB to reduce the dependency between the eNB and EPC is proposed in [2]. A new component called Flexible Management Entity (FME) is suggested to be added to the architecture. The eNB along with the FME which includes the virtual EPC entity would now be called the Hybrid eNB (HYeNB). The detailed design and distributed protocols associated with the FME are discussed in [2]. Wired or wireless technologies such as IEEE 802.11, 802.16, optical, satellite networks, etc. are used to maintain connection between HYeNB and physical EPC. While the above virtualization creates a distributed architecture between the eNB and the EPC, we will discuss about how the dependency between UE and the Radio Access Network (RAN) can be reduced in LTE-A by deploying D2D feature that was introduced in Release 12 of 3GPP [13]. The D2D communication is discovered, established and maintained without any interference from eNB or EPC. The uplink channels PUCCH, PUSCH and PRACH are used for the initialization and operation of the D2D protocol.
A D2D communication can be set up within the UEs in the network when needed either using the D2D-Agent present inside the FME, or the UEs can establish the D2D communication independent of the HYeNB. When connection with eNB is lost for a Time of Interruption (ToI), a selected UE (b-UE) will take up the role of D2D-A. The b-UE will establish, manage and coordinate the D2D network. It is necessary to have ToI to avoid ping-pong effect. The multiple access scheme used by such a b-UE is Single Carrier Frequency Division Multiple Access (SC-FDMA) due to less interference and battery consumption [2].
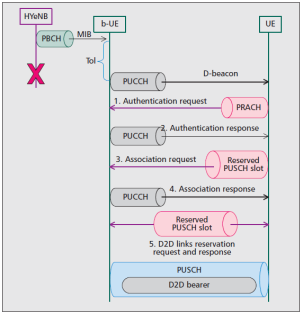
Figure 8. Handshake messages when UE joins a D2D network [2]
All UEs which lost connection with HYeNB for ToI is allowed to consider transmitting direct beacon frames (D-beacons). But before a UE transmits D-beacons, it will listen to the channel for at least two D-beacon time intervals (TD) (time between two beacons which can be any multiple of frame duration 10 ms) to see if any other UE is already the b-UE. If after two TD, no beacon was received, the UE becomes b-UE and starts broadcasting the D-beacons with information such as D2D network ID, identification of UEs in the network, etc. on the Physical Uplink Control Channel (PUCCH). PUCCH is also used by b-UE to reply to UE network association requests as shown in Figure 8 [2]. The network joining procedure is same as the four-way handshake that occurs during LTE random access. There are 64 Zadoff Chu preambles from which the UE who wishes to join chooses from to minimize contention. The contention resolution scenario involves the b-UE sending response based on the UE ID in the D2D network. The UE which did not receive a response backs off. The random access operations are performed using the Physical Random Access Channel (PRACH). The response which is usually sent on Physical Downlink Shared Channel (PDSCH) in traditional LTE, should be sent on PUCCH by the b-UE. Reserved slots in the Physical Uplink Shared Channel (PUSCH) are used for the third message (association request). PUSCH is also used for data and voice transmission. The resources reservation for data and voice takes place between peer UE and does not need b-UE involvement. [2]
The UEs will continue search for synchronization signals and Master Information Block (MIB) on Physical Broadcast Channel (PBCH) to see is the HYeNB has been reconnected. Once reconnected, the resources allocated to the D2D network will be given up [2].
IV. Conclusion
A SON-enabled DRHSCN and D2D communication enabled LTE-A are two technologies that will greatly increase the robustness and resilience of existing cellular networks as well as future 5G networks during disasters. The two methods can be implemented as an overlay by introducing D2D communication within a Heterogeneous network. The multihop smart phone relay using a multiple wireless access and a fusion of routing technology when applied to the D2D network, create another layer of resilience. These methods achieve the primary goal of making the network self-reliant and distributed so that communication can be established even when any part of the network is damaged by disaster. The future 5G architecture can be made disaster-resilient from the start if the proposed methods are taken into account even during standardization. By extending the proposed D2D protocol into Internet of Everything (IoE), we will be able to send emergency messages not only to humans but also to trains, cars, etc. to prevent major accidents.
V. References
- H. Zhang, C. Jiang, R. Q. Hu, Y. Qian, “Self-organization in disaster-resilient heterogeneous small cell networks,” IEEE Network, vol. 30, no. 2, pp. 116-121, 2016.
- K. Gomez, L. Goratti, T. Rasheed, L. Reynaud, “Enabling Disaster-Resilient 4G Mobile Communication Networks,” IEEE Communications Magazine, vol. 52, no. 12, pp. 66-73, Dec. 2014.
- H. Nishiyama, M. Ito, N. Kato, “Relay-by-smartphone: Realizing multihop device-to-device communications,” IEEE Communications Magazine, pp. 56-65, Apr. 2014.
- 3GPP, TSG E-UTRAN, “Self-Configuring and Self-Optimizing Network (SON) Use Cases and Solutions,” TR 36.902 V9.3.1, 2011.
- W. Zheng et al., “Mobility Robustness Optimization in Self-Organizing LTE Femtocell Networks,” EURASIP J. Wireless Commun. , vol. 1, pp. 1-10, 2013.
- H. Zhang et al., “Mobility Robustness Optimization in Femtocell Networks Based on Ant Colony Algorithm,” IEICE Trans. Commun. , vol. 95, no. 4, pp. 1455-58, 2012.
- O.G. Aliu, A. Imran, M.A. Imran, and B. Evans, “A survey of self organisation in future cellular networks,” IEEE Communications Surveys & Tutorials, vol. 15, no. 1, pp.336-361, 2013.
- 3GPP, “Telecommunications management; self-healing OAM; concepts and requirements,” 3GPP TS 32.541 v1.6.1, Tech. Rep., 2010.
- R. M. Khanafer, B. Solana, J. Triola, R. Barco, L. Moltsen, Z. Altman, and P. Lazaro, “Automated diagnosis for UMTS networks using bayesian network approach,” IEEE Trans. Veh. Technol., vol. 57, no. 4, pp. 2451-2461, 2008.
- M. Amirijoo, L. Jorguseski, T. Kurner, R. Litjens, M. Neuland, L. C. Schmelz, and U. Turke, “Cell outage management in LTE networks,” in Proc. 6th Int. Symp. Wireless Communication Systems ISWCS 2009, pp. 600-604, 2009.
- T. Sakano et al., “Disaster-Resilient Networking: A New Vision Based on Movable and Deployable Resource Units,” IEEE Network, vol. 27, no. 4, pp. 40-46, 2013.
- “ICT responses to the Great East Japan Earthquake, FUJINO, Masaru. Counselor for Communications Policy. Embassy of Japan,” U.S. Telecom Assn. Boarding Room, 2011.
- 3GPP, “Feasibility Study for Proximity Services (ProSe)”, TR 22.083, 2012.
- A. Ghosh, N. Mangalvedhe, R. Ratasuk, B. Mondal, M. Cudak, E. Visotsky, T.A. Thomas, J.G. Andrews, P. Xia, H.S. Jo, and H.S. Dhillon, “Heterogeneous cellular networks: From theory to practice”, IEEE Communications Magazine, vol. 50, no. 6, 2012.
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allDMCA / Removal Request
If you are the original writer of this essay and no longer wish to have your work published on UKEssays.com then please click the following link to email our support team:
Request essay removal



